Adding Root Certificates using CERTivity
There are often situations in which we get to a website on a secure connection and the browser informs us that the website's security certificate is not trusted using a warning message similar to the one below (which can be seen when using Google Chrome browser):

This happens mostly when accessing websites of companies that are using internal CA certificates which are self-signed or are not signed by a known and recognized certificate signing authority. To be able to view these kind of websites, the certificate has to be trusted.
When clicking on “Help me understand” link, we will see some additional information about the problem, and in the last paragraph it is explained briefly without any details what should be done to avoid the security warning and access the website safely.
“If, however, you work in an organization that generates its own certificates, and you are trying to connect to an internal website of that organization using such a certificate, you may be able to solve this problem securely. You can import your organization's root certificate as a "root certificate", and then certificates issued or verified by your organization will be trusted and you will not see this error next time you try to connect to an internal website. Contact your organization's help staff for assistance in adding a new root certificate to your computer.“
Although the information is correct, it is not specified how one can import the organization's root certificate as a “root certificate”. More than this, some additional tools might be required to perform the necessary operations (like a tool for retrieving certificates from a SSL server, and a tool for inserting the obtained root certificate into the Windows Root CA KeyStore). Even with Internet Explorer you have to do more operations and export the CA Root certificate in a file, and then import it by opening that file from Windows Explorer and selecting import in one of the many locations. It is easy to get it wrong. This is where CERTivity comes in handy. Using CERTivity, adding a new root certificate to your Windows OS is easier and fast.
The main idea is to obtain the organization's root certificate and to insert it into the Windows Root CA KeyStore. To do that, one has to use the built-in SSL Certificates Retriever function to obtain the root certificate, and to import it into the Windows Root CA KeyStore, which can also be accessed easily through CERTivity. In more details, the simple steps that have to be performed using CERTivity are the following:
- Open the Windows Root CA KeyStore (if not already opened). This can be done very easy in CERTivity, as it has a dedicated menu for that: File > Open > Open Windows Root CA KeyStore.
- While having the Windows Root CA KeyStore opened and focused, open the SSL Certificates Retriever. This can be done using the menu KeyStore > SSL Certificates Retriever (as seen in the screenshot below) or by using the SSL Certificates Retriever button from the toolbar.
 The SSL Certificates Retriever dialog will open allowing the user to retrieve the certificate from server:
The SSL Certificates Retriever dialog will open allowing the user to retrieve the certificate from server:

This dialog allows retrieving certificates either by inserting a HTTPS URL, either by entering the host and port of the server from which the certificate should be retrieved.
When inserting a HTTPS URL, the host and port will be automatically extracted and the “Host name” and “Port” fields will be filled in. The default port used for HTTPS is 443, but a custom port can also be specified by putting it in the URL according to the URL specification.
If the user wants to use a certain host name and port number and does not have a HTTPS URL, he can do that by selecting the second radio button below “URL (HTTPS)”, which will enable the “Host Name” and “Port” fields, and inserting or modifying the host name or port number according to his desire.After providing the required information, press “Retrieve certificates” button. In this example the URL https://jira.edulib.ro was used for retrieving the certificates: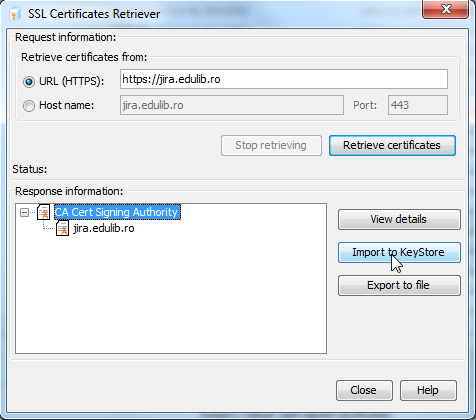
In this case, the response from the server is actually a chain of certificates, which starts with the organization's root certificate - “CA Cert Signing Authority” which we need to import into the Windows Root CA KeyStore. Any of the certificates from the chain can be imported as well if needed.
- Select the certificate to be imported into the Windows Root CA KeyStore and press “Import to KeyStore”. The user will be prompted to enter an alias for the certificate. The name of the certificate will be used as a suggestion.

When importing a certificate into the Windows Root CA KeyStore, there is a security warning displayed by the operating system informing that a certificate will be installed, and asking for the user's permission:
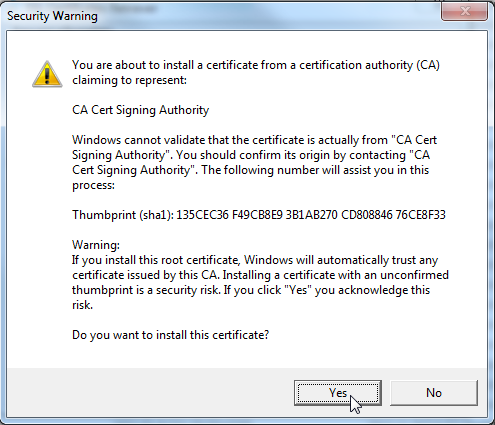
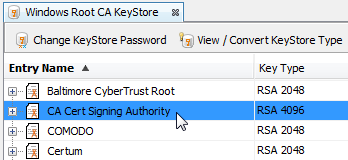
After clicking “Yes”, the certificate will be imported into the Windows Root CA KeyStore. The Open SSL Certificate Retriever dialog can be closed now by pressing “Close”.The new imported certificate will be visible into the Windows Root CA KeyStore, as it can be seen in the screenshot below:
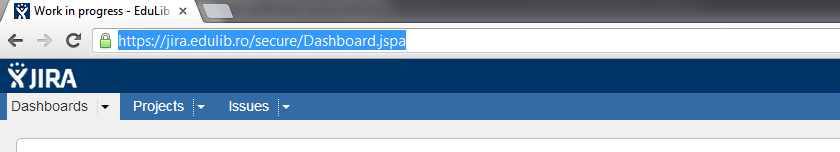
- After performing these simple steps to import the certificate, restart the browser for the changes to take effect. The security warning will no longer be displayed allowing to view the desired website.
The organization root certificate can also be imported in a similar way into the Windows Root CA KeyStore from a different KeyStore if it exists already in a KeyStore using copy – paste operations. Also, it can be copied from a KeyPair, in a way similar to the one described in the post Simplifying key pair and certificate management operations with CERTivity.