Simplifying Key Pair and Certificate Management Operations with CERTivity
The usage of electronic services such as electronic banking, electronic commerce or virtual mails becomes more commonplace in the present. Therefore there is an increasing need for using digital certificates to establish authenticity, digital signatures, or encryption of personal data. This requires the ability to handle cryptographic material such as private / public key pairs, secret keys, or digital certificates, in other words, the ability to create key pairs and store them into different keystores, or exporting only the certificate into another keystore, the possibility to use a private key to digitally sign a document, and many others. These can be achieved easily using CERTivity due to its intuitive GUI and structure.
The following scenario can give a hint of how easy it is to work with key pairs and certificates in CERTivity.
The user wants to generate a self-signed key pair, store it into a KeyStore, and then, copy only the certificate from the self-signed key pair and store it into a different keystore (for example the cacerts keystore, or another truststore like the Windows Root CA KeyStore).
Such a scenario can be found frequently in real life. For example, we can suppose we have a server in Java and we need to connect with a Windows Client (which could simply be the browser or a custom Windows client) and the SSL layer is used. When using connections over the SSL layer, the authentication is performed using a private key and a public key. Usually the private key resides on the server side, while the public key is found on the client side. So that is why, it is important that after creating a key pair to be able to separate the private keys and certificates easily (as the certificates contain the public key).
The above mentioned scenario can be performed with other existing tools as well, but the steps needed to accomplish this would require creating the key pair and storing it into the keystore, then exporting the certificate into a file and then importing it again from the file into the truststore.
In CERTivity, this can be done in few steps without using any auxiliary files or export and import operations, just clipboard operations. We will consider that the KeyStore into which the key pair will be generated is opened and it is called “my-keypairs.jks”, and that we will want to copy the certificate into the Windows Root KeyStore.
The steps are the followings:
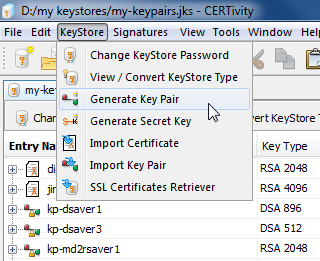
- Create a new self-signed key pair. Having the “my-keypairs.jks” keystore opened and focused, use the menu KeyStore > Generate Key Pair, or the Generate Key Pair toolbar button to open the dialog for creating new self-signed key pairs.
The following dialog appears, allowing the user to provide the needed information for generating the keys and the certificate.

- Expand the newly created key pair node in the KeyStore (by clicking on the “+” sign in front of the key pair entry), and also expand the Certificates Chain node. The new generated certificate will be visible.
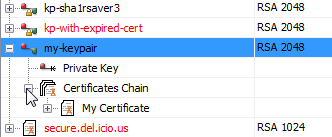
- Select the certificate node and copy it (by right clicking on it and selecting the Copy menu, or by using the CTRL + C shortcut.

- Open the Windows Root CA KeyStore. This can be done very easy in CERTivity, as it has a dedicated menu for that: File > Open > Open Windows Root CA KeyStore.
- Having the Windows Root CA KeyStore opened and focused, paste the copied certificate node (by using CTRL + V or Edit > Pastemenu. When inserting a certificate into the Windows Root CA KeyStore, there is a security warning displayed by the operating system informing that a certificate will be installed, and asking for the user's permission:

After clicking yes, the certificate will be imported into the Windows Root CA KeyStore, as it can be seen in the screenshot below:

As it could be seen, to accomplish the above scenario, no “export to file” and “import from file” operations were needed, so this eases the work of the user a lot. In the example above we used for the trust store the Windows Root CA KeyStore, but the steps are the same for any other KeyStore, with the exception of the security warning issued by the Windows operating sistem, which only appears on Windows systems when inserting a certificate in to the Windows Root CA Truststore.
This was only one simple example of how things can be done easier using CERTivity, due to its user-friendly GUI, the way it is organized and due to the features that it provides, but there can be many more.